In today’s digital landscape, cyber threats are not a matter of “if” but “when.” The increasing frequency and complexity of attacks make it essential for organizations to stay vigilant and prepared. By adopting proactive measures, companies can respond quickly to cybersecurity incidents, minimize damage, and maintain business continuity. Leveraging an expert-led incident response service can further strengthen your ability to handle crises, ensuring vital systems and data are protected.
Preparation is critical for successful incident response. Organizations that implement structured processes and train their teams in advance are far better positioned to recover swiftly from an attack. Addressing potential threats before they escalate can help preserve an organization’s reputation and maintain client trust, which are essential in today’s connected environment. Every organization, regardless of size or industry, faces evolving threats that can exploit unguarded vulnerabilities. There is no single solution for cyber risk, but by layering multiple strategies, you can make your defenses much harder to penetrate. While no defense is perfect, readiness can often make the difference between a minor disruption and a devastating data breach. Organizations that excel in incident response embrace a blend of technology and teamwork. Taking a broad approach, including team training, regular policy reviews, and the adoption of emerging security technologies, can greatly increase resilience against cyberattacks.
Establish a Comprehensive Incident Response Plan
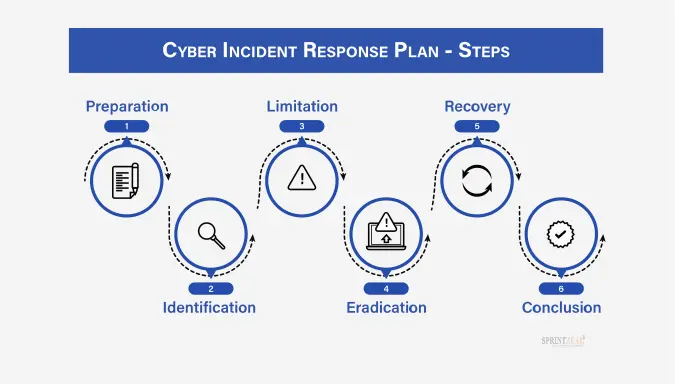
A robust incident response plan (IRP) acts as an organizational roadmap during a security crisis. This plan must detail the exact steps to take, assign responsibilities to specific team members, and establish communication methods with both internal and external stakeholders. By defining contact points and escalation paths, businesses can rapidly contain threats and avoid confusion during high-pressure events.
- Step-by-step response protocols for various scenarios
- Clearly defined roles and responsibilities
- Effective communication strategies for all relevant audiences
Regular IRP updates and practice drills are essential, guaranteeing the plan’s effectiveness when a real attack unfolds.
Conduct Regular Training and Simulations
Human mistakes remain a weak link in organizational cybersecurity. Employees at every level must receive ongoing training to recognize and report suspicious activities. Simulated phishing campaigns and tabletop exercises sharpen skills, improve reaction time, and reveal knowledge gaps. This approach supports a culture of security awareness across the organization.
- Mandatory cybersecurity awareness for all employees
- Simulated phishing campaigns to identify vulnerabilities
- Enforcement of multi-factor authentication (MFA) and robust password policies
Training reduces the risk of falling victim to attackers seeking to exploit human behaviour, and it fosters a shared sense of responsibility for protecting company assets.
Implement Robust Security Measures
Regardless of preparation, organizations must maintain strong security fundamentals to reduce the likelihood of incidents. Multi-factor authentication adds a crucial barrier for unauthorized access, while advanced firewalls and next-generation antivirus software provide real-time detection and response capabilities. Regular vulnerability assessments identify and close gaps before attackers can exploit them.
- Mandatory multi-factor authentication for all sensitive systems
- Next-generation antivirus and firewall technologies are updated regularly
- Scheduled vulnerability assessments and penetration testing
Consistently evaluating defenses not only protects your network but also demonstrates diligence if regulatory bodies ever review incidents. For more information on effective defense strategies, visit the Cybersecurity & Infrastructure Security Agency.
Monitor for Emerging Threats
Cyber adversaries are constantly developing new methods to breach defenses. Staying current with the latest intelligence is critical for organizations of all sizes. This often involves subscribing to threat feeds, participating in security councils, and building relationships across your industry. Collaboration increases situational awareness and provides early warnings about widespread attacks or new vulnerabilities.
- Real-time threat intelligence monitoring
- Active participation in industry-specific forums and cybersecurity communities
- Peer collaboration for information sharing
Effective threat monitoring and response efforts have been recommended by global cybersecurity, leaders such as Kaspersky, underscoring the importance of continuous vigilance and information exchange.
Establish Clear Communication Channels
During a cybersecurity incident, timely and transparent communication can make a major difference in outcomes. Having pre-approved messaging helps organizations quickly inform customers, regulators, and stakeholders, promoting calm and trust rather than uncertainty. An appointed spokesperson ensures the accuracy and consistency of public statements while preventing the release of sensitive details that could further harm the organization.
- Prompt customer and regulator notifications
- Utilization of approved messaging templates
- Designated spokesperson for clear communication
Clearly documented communication processes maintain public confidence and demonstrate accountability and transparency at every stage of incident response.
Engage with Incident Response Partners
Maintaining relationships with specialized incident response vendors, forensic experts, and legal advisors guarantees rapid external support when a major crisis hits. These partners lend expertise in complex incident investigations, help preserve forensic evidence, and provide guidance on regulatory disclosures and liability management. Having reliable contacts on standby enables organizations to expedite recovery while minimizing long-term impact.
Review and Update Policies Regularly
Cyber threats evolve, and so must your organization’s defenses. Reviewing and updating policies regularly ensures that security controls remain effective and relevant. This ongoing process enables quick adaptation to emerging attack vectors, newly discovered vulnerabilities, and regulatory or industry-standard changes. A proactive policy review process supports ongoing improvement and delivers long-term protection for both data and operations.
Conclusion
By building a comprehensive proactive strategy, organizations significantly enhance their resilience to cyber threats and reduce the potential impact of attacks. A blend of preparedness, training, advanced technology, and strong partner relationships sets the foundation for robust incident response. Prioritizing strong defenses not only reduces risk but also solidifies client and stakeholder trust, safeguarding your business now and into the future.