Modern enterprises face a rapidly evolving cyber threat landscape, where adversaries employ increasingly sophisticated tactics to compromise sensitive data, disrupt critical operations, and undermine brand trust. As organizations expand their digital footprint, moving operations to the cloud, working with remote teams, and deploying new digital services, the demand for robust, effective security strategies has never been higher. Without proper measures, even a single breach can lead to devastating financial loss, operational downtime, and lasting reputational damage. Adopting managed network security services can provide not just a first line of defense, but a comprehensive system of controls and expert oversight. These services help organizations safeguard critical digital assets, prevent costly breaches, and ensure uninterrupted business continuity amid persistent, ever-changing cyber risks.
Security leaders now recognize that traditional reactive approaches, which focus on responding to incidents only after they occur, are no longer sufficient in today’s complex threat landscape. Attackers are faster, more agile, and increasingly targeting weak links across the digital ecosystem. As a result, a comprehensive, proactive readiness strategy has become essential to mitigate risk and enhance resilience across all layers of the enterprise. This approach involves layering advanced technologies, automating threat detection and response, establishing cross-functional processes, and empowering every employee to act as a vigilant part of the security fabric. Such holistic readiness enables enterprises not only to defend against known threats but also to adapt to emerging risks.
Understanding the Current Cyber Threat Landscape
The current threat landscape is more complex and varied than ever before. According to a recent study, only 3% of businesses have attained the maturity level required to effectively defend against today’s advanced cyber threats. Attackers are not just targeting large corporations; small and midsize businesses are also at risk, especially those with limited resources and outdated defenses. Malicious actors exploit vulnerabilities across supply chains, endpoints, cloud infrastructure, and networks, often utilizing advanced methods such as ransomware, credential theft, phishing, and zero-day exploits. The alarming statistic that so few enterprises are adequately prepared underscores the urgency for all organizations to regularly reassess their cybersecurity posture and promptly address any resilience gaps.
For organizations with relatively mature cybersecurity programs, the sheer volume and variety of new threats, ranging from sophisticated nation-state attackers to opportunistic cybercriminals, necessitate continuous monitoring and rapid adaptation. Businesses cannot afford to focus solely on external risks; internal vulnerabilities, often overlooked due to a lack of awareness, budget constraints, or resource limitations, also pose significant risk. This dual necessity for vigilance against both external and insider threats means that comprehensive detection, response, and risk management should be at the core of every enterprise’s security strategy.
Implementing Continuous Threat Exposure Management
One of the most critical components of an effective readiness strategy today is adopting Continuous Threat Exposure Management (CTEM). Unlike traditional vulnerability management that relies on periodic assessments, CTEM delivers real-time identification, assessment, prioritization, and remediation of vulnerabilities before adversaries have a chance to act. By proactively simulating likely attack scenarios, security teams can identify exploitable weak points across infrastructure, applications, and user accounts. This dynamic process helps organizations stay ahead of threat actors and shorten the time between vulnerability discovery and remediation. CTEM systems provide the agility required for modern defense, as they are designed to evolve alongside the rapidly-changing threat environment.
Implementing CTEM often includes automated scanning tools, simulated attack campaigns like red teaming, and integrations with incident response workflows. The goal is to continuously gauge the attack surface, prioritize threats by risk, and accelerate the entire remediation process. By continuously improving threat visibility and readiness, organizations can make better-informed decisions and allocate their security resources where they are most needed.
Empowering Employees Through Training
Since up to 95% of cyber incidents are attributed to human error, security awareness and comprehensive training programs must be a top priority for enterprises of all sizes. Employees are often the first line of defense and sometimes the weakest link in preventing security incidents, from unwittingly clicking on malicious links to falling prey to social engineering attacks. Organizations that invest in ongoing, role-based security training empower their workforce to spot and respond to suspicious activities, reduce the risk of accidental data leakage, and foster a shared sense of responsibility for protecting sensitive information. Effective training programs typically include simulated phishing tests, interactive modules tailored to specific risks and roles, and clear incident-reporting processes.
Regular security drills and feedback sessions can further reinforce best practices, helping to transform security from a compliance checkbox into a core business value. Ultimately, an educated and engaged workforce is far less likely to make costly mistakes and more likely to act as a critical component of the organization’s layered defense strategy.
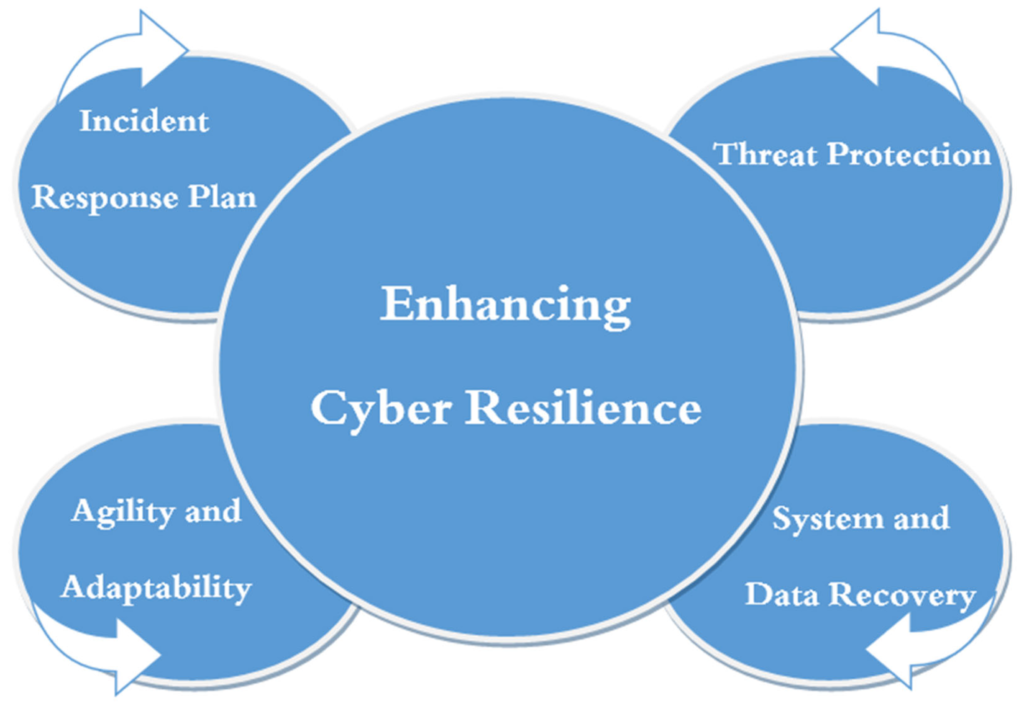
Developing a Comprehensive Incident Response Plan
An Incident Response Plan (IRP) is indispensable for minimizing chaos and limiting damage in the aftermath of a security breach or cyber event. A well-crafted IRP outlines detailed, step-by-step procedures for rapidly identifying, containing, eradicating, and recovering from an incident. The most effective response plans are not static documents; they are regularly tested and updated to reflect the evolving threat landscape. Regular drills, tabletop exercises, and real-world simulations ensure that employees and stakeholders know exactly what to do under pressure. Involving all key departments from IT and cybersecurity specialists to public relations, legal, and executive leadership guarantees a coordinated response that can minimize business, reputational, and regulatory impact.
Moreover, organizations should embed incident response planning into their overall risk management framework, making it a living process that adapts and improves over time. Post-incident reviews, root cause analysis, and lessons learned help to continually strengthen defenses and reduce the likelihood of recurrence.
Leveraging Artificial Intelligence in Cybersecurity
Artificial Intelligence (AI) has rapidly emerged as a game-changer for organizations seeking to defend against increasingly complex, high-speed cyberattacks. AI-powered security tools excel at analyzing vast, diverse datasets in real time, flagging outliers and emerging threats that traditional tools or human analysts might miss. Powerful machine learning models can identify subtle anomalies in network traffic, user behavior, or system processes that suggest malicious activity, and they do so much faster than manual methods. As they face more threats, AI-driven solutions continuously adapt to new techniques, improving both detection rates and response times. This advanced intelligence can automate much of the tedious analysis and incident escalation, freeing up human experts to focus on higher-level investigation, strategic planning, and proactive defense.
By combining AI tools with human expertise, organizations can gain better visibility into underlying threats, accelerate response, and drastically improve their chances of mitigating cyber risks before they escalate.
Adopting a Zero-Trust Security Model
A zero-trust security framework is based on the principle that no user, device, or system, whether inside or outside the network perimeter, should be inherently trusted. Every access request is carefully authenticated, authorized, and monitored, regardless of whether it originates from inside the corporate network or a remote location. This greatly minimizes the “blast radius” of any compromised credentials or breached endpoint. By segmenting access, least-privilege policies ensure that users have access only to the resources they need, and nothing more. Continuous identity verification and encrypted connections further reduce the risk of lateral movement and unauthorized data exfiltration within enterprise environments. Adopting zero trust is a powerful way to limit exposure, especially as more organizations embrace hybrid work environments and cloud-first strategies.
Regularly Updating and Testing Security Measures
In cybersecurity, strategies and controls must never be static. Threats evolve constantly, and new vulnerabilities emerge nearly daily. Enterprises must commit to regularly testing, updating, and improving their defensive measures, including conducting penetration testing, vulnerability scanning, and security assessments as part of routine operations. This ongoing evaluation uncovers hidden weaknesses, validates existing controls, and ensures that the latest patches and configurations are applied across the board. By fostering a culture of continuous improvement, organizations not only stay ahead of threats but also remain compliant with increasing regulatory demands and industry best practices. Ultimately, adaptive security postures are both a technical requirement and a mindset for sustainable business operations.
Conclusion
Enterprises today must move decisively beyond basic, perimeter-focused defenses to adopt a holistic, proactive approach to cyber readiness. By harnessing the power of managed network security services and integrating frameworks such as Continuous Threat Exposure Management, comprehensive employee education, AI-driven threat detection, and a zero-trust security architecture, organizations can significantly increase their resilience and agility. No matter how the threat landscape continues to shift, deploying an integrated, layered security strategy anchored in best practices and continuous improvement will equip enterprises to protect their assets, retain customer trust, and maintain operational stability now and in the future.